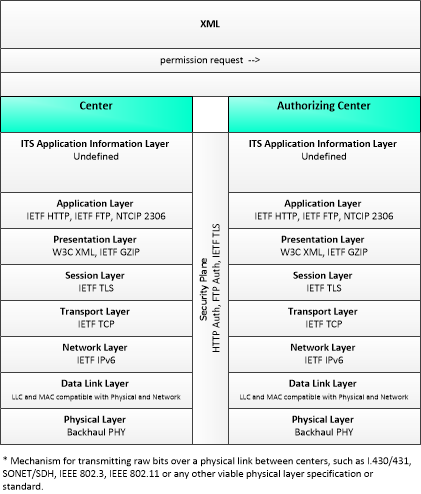
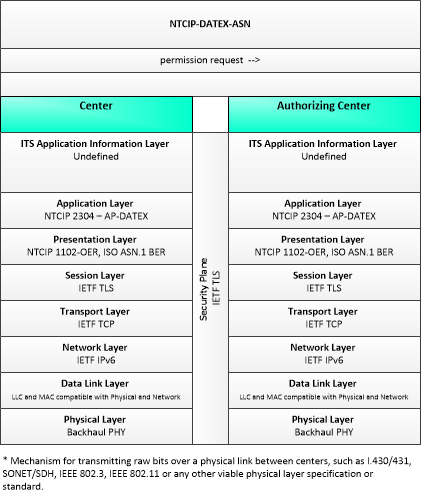
Link Type: Center to Center
Center --> Authorizing Center:
permission request
Definitions
permission request (Information Flow): A request for permission to access or use connected vehicle applications or services. The request identifies the users that require permission, the applications or services that are requested, and the geographic coverage where the permission is required. In this context, the 'users' may be a center, infrastructure equipment (e.g., RSEs), or vehicles that are owned and operated by the requestor. This request is for an initial set of permissions. See also permission update request.
Center (Source Physical Object): This general physical object is used to model core capabilities that are common to any center.
Authorizing Center (Destination Physical Object): The 'Authorizing Center' provides the functionality needed to enable data exchange between and among mobile and fixed transportation users. Its primary mission is to enable safety, mobility and environmental communications-based applications for both mobile and non-mobile users. The Authorizing Center has some jurisdiction over limited access resources; typically this includes roadside application access and radio spectrum licensing. It may be implemented as an autonomous center or as a set of supporting services that are co-located within another center.
Included In
This Information Flow is in the following Applications:
This Information Flow is in the following Application Objects:
Communication Diagrams
The communication diagram(s) can be viewed in SVG or PNG format and the current format is SVG. Switch to PNG format.
This profile describes an alternative set of standards applicable to communications between entities using ISO TC204 WG9 DATa Exchange(DATEX). Information messages are encoded using the NTCIP Octet Encoding Rules (OER).
Characteristics
Architectural:
| Characteristic | Value |
|---|---|
| Time Context | Static |
| Spatial Context | Regional |
| Acknowledgement | True |
| Cardinality | Unicast |
| Initiator | Source |
Security
This information flow triple is in the following applications with the following security levels.
| Information Flow Security | |||||
|---|---|---|---|---|---|
| Application | Confidentiality | Integrity | Availability | ||
| Basis | Basis | Basis | |||
| Security levels have not been defined yet. | |||||